![[Guide] Permission Required from TrustedInstaller](https://cdn.techloris.com/app/uploads/2023/04/A-Guide-to-Follow-if-You-Require-Permission-From-TrustedInstaller.png)
[Guide] Permission Required from TrustedInstaller
What is TrustedInstaller?
TrustedInstaller is an inbuilt user account present and one of the core components of Windows Resource Protection in Windows operating systems that performs a range of system-related functions such as installing system updates, modifying system files and registry keys, and managing system-level permissions. Its design gives it exceptional access and privileges, enabling it to make critical changes to the system components.
Microsoft introduced the TrustedInstaller account with Windows Vista to enhance the security and stability of the operating system. Previously, users had administrative-level access to their systems, exposing them to security threats like malware.
A significant advantage of using the TrustedInstaller account is that it prevents unauthorized modifications to crucial system files and settings. With its elevated access levels, it can supersede other user accounts and ensure that only authorized changes are made to the system. This helps maintain the security and integrity of the operating system.
Where Can I Find Trustedinstaller?
1. Press Win + E to open the File Explorer.
2. Paste the following path into the address bar and press Enter.
C:\Windows\servicing
3. You will see the Trustedinstaller.exe application.

The Windows Module Installer service, known as TrustedInstaller.exe, is responsible for installing, modifying, and uninstalling system components and updates within the Windows operating system.
How Can You Require Permission From Trustedinstaller on Windows?
Using Command Prompt
1. Press the Windows key and type cmd.
2. Select the Command prompt and run as an administrator.

3. Type the following command to take control of a particular file and press enter:
TAKEOWN /F “c:\Program Files\Windows Defender\MS.”

4. It is important to change and enter the full file name and path without any parentheses.
5. You should see Success: The file (or folder): “filename” is now owned by user “Computer Name/User Name.”
Take Ownership From Trustedinstaller Using File Explorer
1. Press Win + E to open File Explorer.
2. Right-click on the folder or file you want to own.
3. Select Properties.

4. Go to the Security tab and click the Advanced button on the Properties window.

5. Click the Change Permissions button in the Advanced Security Settings window.
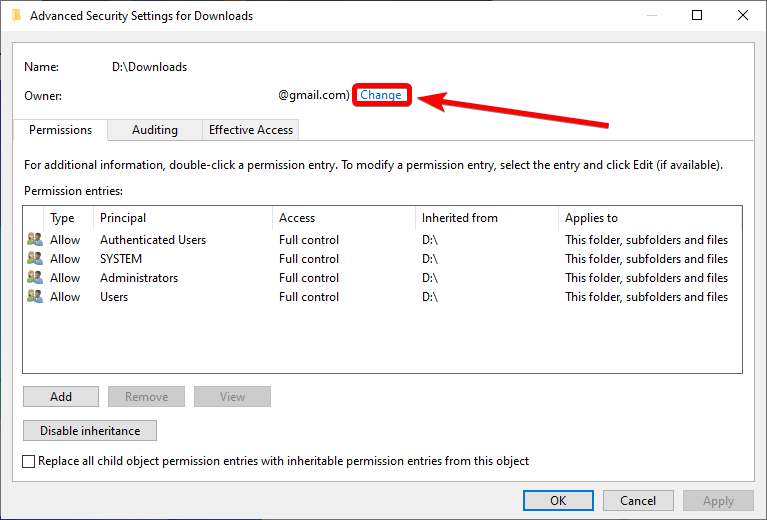
6. Under Enter the object name to select, input your user account name.
7. Click the Check Names button. If you can’t find your username, you can search for it manually in the lists of users.

8. Check Replace owner on sub containers and objects box.
9. Click Apply, close the Advanced security settings window, and reopen it.
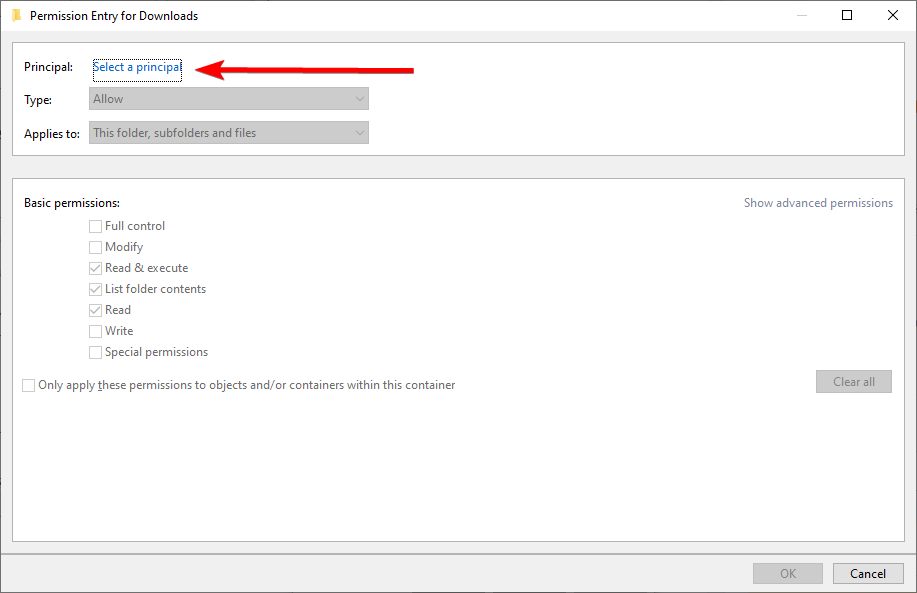
10. Click the Add button.

11. Click on Select a Principal, enter your username, check all the permission boxes, then click the OK button.
12. Check to Replace all child object permission entries with inheritable permission entries from this object box and click the Apply button.

Run the System File Checker (SFC Scan)
In this tool, Windows scans and repairs corrupted system files, including those associated with the TrustedInstaller account. By running SFC, you can restore the integrity of your system files, fix the TrustedInstaller problem, and gain permission to modify or delete the files you need.
1. Open the Start menu and type cmd.
2. Run the Command prompt as an administrator.

3. Type the following command and press Enter:
sfc /scannow
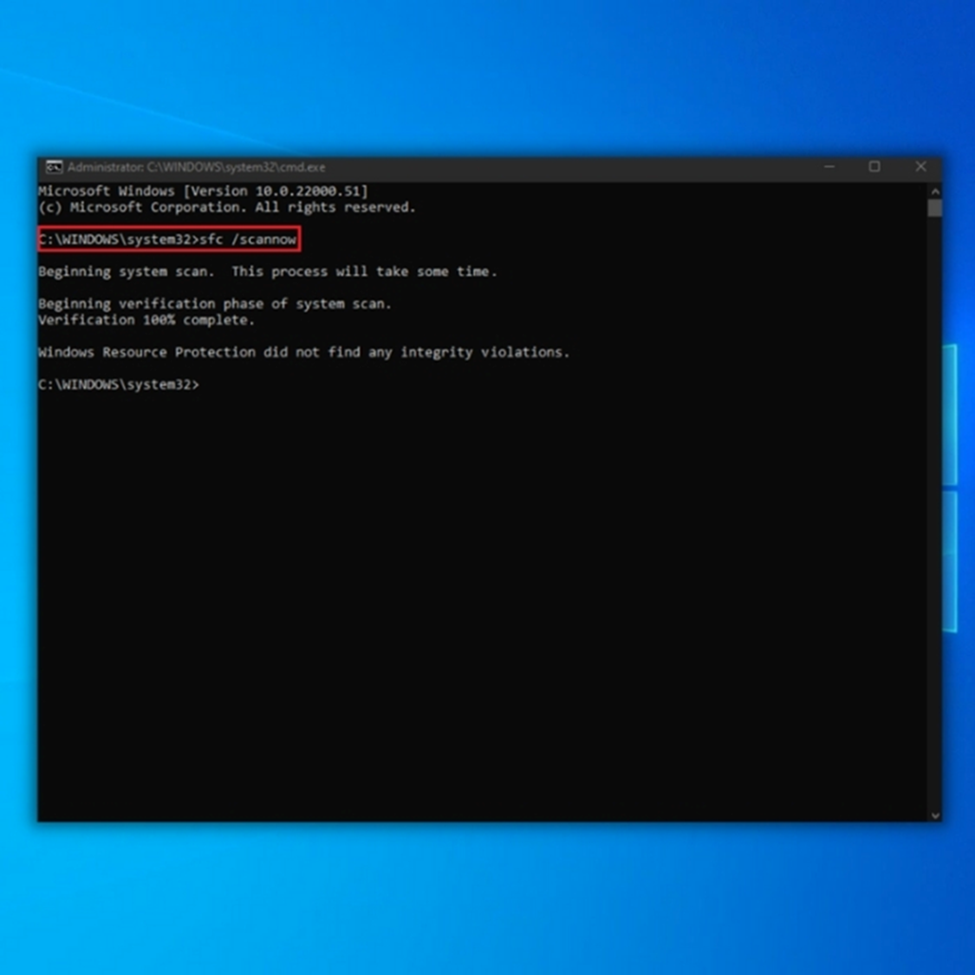
4. Restart your computer.
Use a System Restore Point
When attempting to modify or delete specific system files or folders on a Windows computer, you may encounter an error message that says, “You require permission from TrustedInstaller to make changes to this file/folder.” This error occurs because the TrustedInstaller account owns these files and folders and has exclusive permission to modify or delete them.
One potential solution to this problem is to use System Restore. System Restore is a built-in Windows feature that allows you to revert your computer’s settings to a previous time. This means you can use System Restore to restore your computer to a state where you can modify or delete the files or folders.
1. Open the Start menu and type Recovery.
2. Open Recovery.

3. Select Open System Restore.

4. Follow on-screen instructions.
5. You can choose a restore point yourself or select Recommended restore.

6. Click the Next button, then Finish.
Run a Malware Scan
Running a malware scan is a simple process that involves downloading and installing a reputable antivirus or anti-malware program and initiating a full system scan. The software will then search for and remove any malware detected on your computer, including any malicious programs that may interfere with your ability to modify or delete system files.
1. Open the Start menu and type security.
2. Select and open Windows Security.
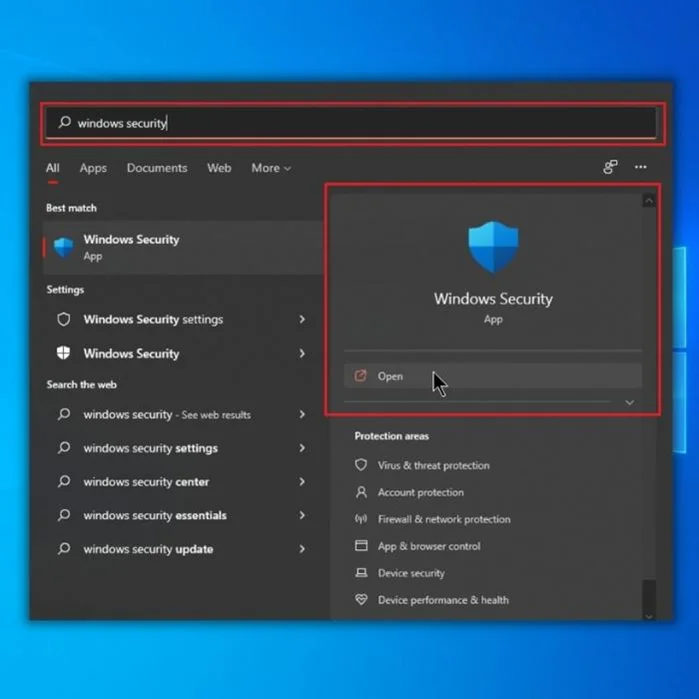
3. Go to Virus & Protection tab and click on Scan options.
4. Select the Full Scan option and click the Scan Now button.

Granting Permissions with Confidence: A Guide to TrustedInstaller
In this comprehensive guide, we explored the issue of permissions required from TrustedInstaller and provided practical solutions to navigate this challenge. By following the step-by-step instructions and understanding the role of TrustedInstaller, you can confidently manage permissions on your Windows system. Whether you need to modify system files or install software, the methods outlined in this guide will help you gain the necessary permissions while maintaining system integrity.
With the knowledge gained from this guide, you can effectively address the TrustedInstaller permissions issue and take control of your system’s access rights. Say goodbye to permission roadblocks and enjoy a smoother and more customizable computing experience. By empowering yourself with the techniques presented here, you can ensure that your actions are executed precisely and securely, confidently granting permissions.
Frequently Asked Questions About “You Require Permission From Trustedinstaller”
Does the Security Tab Affect Permission Requirements From Trustedinstaller?
The Security tab in Windows allows users to control permissions on files and folders. It can be used to grant or restrict access to certain areas of the system. However, it is essential to note that this only affects user-level permissions, not those of TrustedInstaller. TrustedInstaller is an account built into the Windows operating system that controls permission levels on certain files and folders.
Does Each User Account Have Different Permissions From Installers?
Yes, each user account has different permissions from installers. Installer accounts have more privileges than other users since they can modify the system and perform administrative tasks. User accounts are granted more limited access to the computer, including access to data and applications but not total control over the operating system.
Do Permissions Affect Protected Files on Windows?
Yes, file permissions can affect protected files in Windows. When a user has access to specific files, they can view and edit them as they please, regardless of the protection setup. However, if a user cannot access these files, any attempts to modify or delete them will be blocked.
Why Does Permission From Trustedinstaller Show During Windows Updates?
Sometimes, users may be presented with a dialog box containing “trustedInstaller” as the user listed during Windows updates. TrustedInstaller is a feature in Windows that provides enhanced security by allowing only certain accounts to alter existing files or replace them with newer versions.
What Is a Permission Entry Window?
A Permission Entry Window is a feature that allows users to grant permissions to websites or web applications. This is usually done to grant access to sensitive data, such as banking information, medical records, etc. The window gives users the necessary controls to manage the user-level permissions for any website or application.
Why Can’t I Obtain Folder Access From Trustedinstaller?
TrustedInstaller is a service built-in into the Windows operating system that controls access to certain folders and files. It is used to protect sensitive areas of the system that are critical for its proper functioning. As such, TrustedInstaller does not provide users with folder access rights by default due to security concerns.
Can I Have Full Control Over Permissions From One User Account?
Yes, it is possible to have full control over permissions from one user account. This can be done by setting the appropriate permission settings for that user within your system. For example, a Windows computer administrator account has full control and complete access to all files and folders in the system, including managing permissions for other users.
What Are Core Windows Files?
Core Windows files are folders and files that serve as the foundation of the Windows operating system. They include essential elements like System32, which contains important components such as Dynamic Link Libraries (DLLs) and system drivers, and user interface items like Program Files, which holds all installed program data.

![[Windows Guide] How to Access Temp Files in Windows 10](https://cdn.techloris.com/app/uploads/2023/03/How-to-Access-Temp-Files-in-Windows-10.png)
![[Full Guide] How to Remove Windows Old Files from Windows](https://cdn.techloris.com/app/uploads/2023/01/remove-windows-old-files-from-pc-1.png)

