Recommended: Use Fortect System Repair to repair A8d80158-8a89-4bce-b3c5-45be4ebf96dd-4.exe errors. This repair tool has been proven to identify and fix errors and other Windows problems with high efficiency. Download Fortect here.
- ✓
If you're having trouble with the a8d80158-8a89-4bce-b3c5-45be4ebf96dd-4.exe file, you're not alone. This article will help you understand common errors and how to fix them. We'll also cover ways to troubleshoot malware and safely uninstall any related software.
Let's get started!
Common A8d80158-8a89-4bce-b3c5-45be4ebf96dd-4.exe Errors on Windows
Dealing with a8d80158-8a89-4bce-b3c5-45be4ebf96dd-4.exe errors can often be perplexing, given the variety of issues that might cause them. They can range from a mere software glitch to a more serious malware intrusion. Here, we've compiled a list of the most common errors associated with a8d80158-8a89-4bce-b3c5-45be4ebf96dd-4.exe to help you navigate and possibly fix these issues.
- A8d80158-8a89-4bce-b3c5-45be4ebf96dd-4.exe has Stopped Working: This alert appears when the executable file ceases to operate correctly. Potential causes could include software glitches, incompatibilities with other software, or insufficient system resources.
- Unable to Start Correctly (0xc000007b): This error usually occurs when a user tries to run applications that are designed to run on non-compatible versions of Windows.
- Runtime Errors: This alert appears when a program experiences a difficulty while running. Potential causes could include coding errors, memory overflows, or interference from other software currently in operation.
- A8d80158-8a89-4bce-b3c5-45be4ebf96dd-4.exe Application Error: This warning appears when the executable application faces a difficulty during its operation. This could be brought about by software errors, damaged associated files, or clashes with other running programs.
- Insufficient System Resources Exist to Complete the Requested Service: This error message shows up when the system lacks the necessary resources to carry out the service requested, possibly due to overuse of system memory or high CPU usage.
File Analysis: Is A8d80158-8a89-4bce-b3c5-45be4ebf96dd-4.exe a Virus?
Potential safety concerns surround the file a8d80158-8a89-4bce-b3c5-45be4ebf96dd-4.exe, flagged by 37 virus scanners. This doesn't mean your system is infected, but it suggests caution with this file to prevent unauthorized access or system issues.
Recommended Solution: Fortect
To secure your system, we recommend Fortect, a trusted malware scanner.
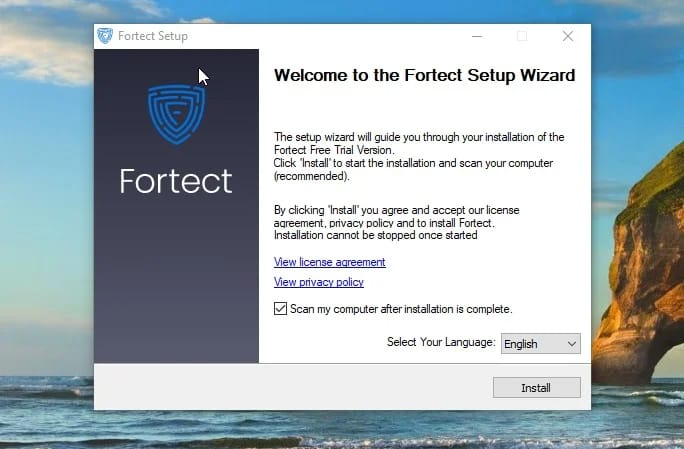
How to use Fortect::** Download: Click the download button to download Fortect.
- Install: Open the downloaded file to start the installation process. Follow the prompts on your screen.
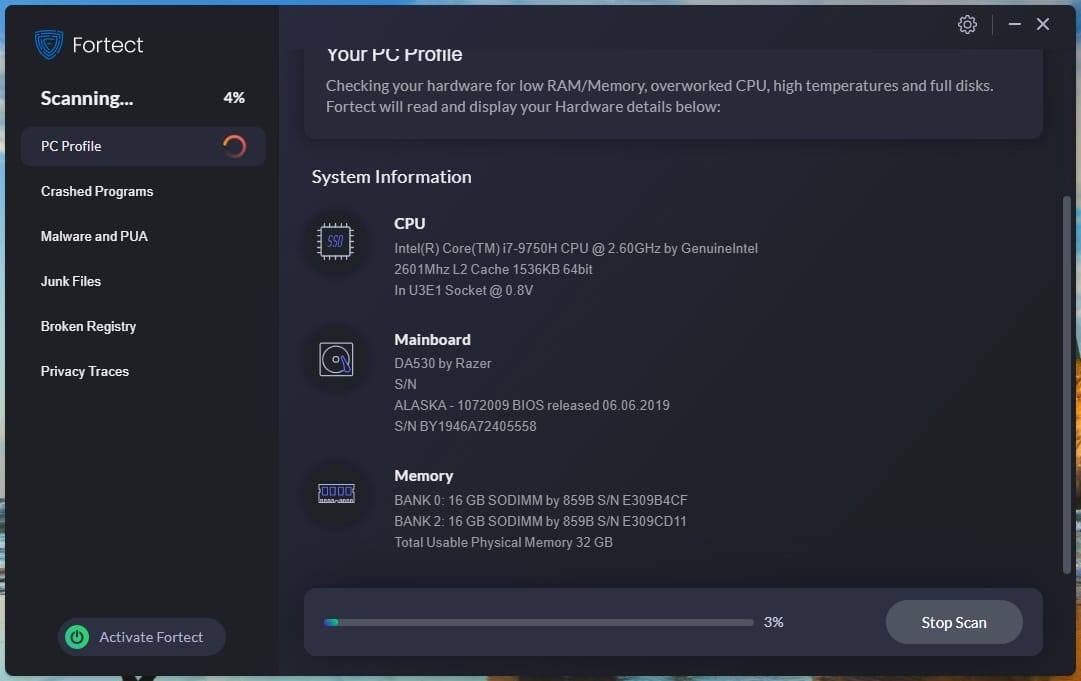
- Scan: Once installed, run Fortect. It will scan your system for harmful files like a8d80158-8a89-4bce-b3c5-45be4ebf96dd-4.exe and fix any identified issues.
Multiple virus scanners have detected possible malware in 1 variations of a8d80158-8a89-4bce-b3c5-45be4ebf96dd-4.exe.
| Scanner Software | Version | Result |
|---|---|---|
| AhnLab-V3 | 2014.10.13.02 | PUP/Win32.CrossRider |
| avast! | 8.0.1489.320 | Win32:Crossrider-AI [PUP] |
| AVG | 14.0.0.4040 | Berta.0DE |
| AVware | 1.5.0.16 | Crossrider (fs) |
| Clam AntiVirus | 0.98.4.0 | Win.Adware.Crossrider-31 |
| Dr.Web | 7.0.10.8210 | Trojan.Crossrider.33417 |
| ESET-NOD32 | 10553 | a variant of Win32/Toolbar.CrossRider.AV |
| F-Prot | 4.7.1.166 | W32/A-2da5f9d7!Eldorado |
| Malwarebytes | 1.75.0.1 | PUP.Optional.WinService.A |
| NANO AntiVirus | 0.28.2.62483 | Trojan.Win32.Crossrider.dfifgb |
| Panda Antivirus | 10.0.4.2 | Trj/Genetic.gen |
| Symantec | 20141.1.0.330 | Adware.Crossid |
| VIPRE Antivirus | 33878 | Crossrider (fs) |
| Zillya | 2.0.0.1953 | Trojan.GoogUpdate.Win32.3491 |
| Lavasoft Ad-Aware | 12.0.163.0 | Gen:Variant.Adware.Kazy.132996 |
| Bitdefender | 7.2 | Gen:Variant.Adware.Kazy.132996 |
| Emsisoft Anti-Malware | 3.0.0.600 | Gen:Variant.Adware.Kazy.132996 (B) |
| F-Secure | 11.0.19100.45 | Gen:Variant.Adware.Kazy.132996 |
| G Data | 24 | Gen:Variant.Adware.Kazy.132996 |
| MicroWorld-eScan | 12.0.250.0 | Gen:Variant.Adware.Kazy.132996 |
| Avira | 7.11.178.166 | ADWARE/CrossRider.Gen4 |
| Baidu-International | 3.5.1.41473 | PUA.Win32.CrossRider.BAV |
| McAfee | 6.0.5.614 | Artemis!1EE4D71D85E7 |
| McAfee-GW-Edition | v2014.2 | BehavesLike.Win32.BadFile.th |
| Sophos | 4.98.0 | Generic PUA HI |
| Vba32 AntiVirus | 3.12.26.3 | Trojan.GoogUpdate |
| IKARUS anti.virus | T3.1.7.8.0 | PUA.VideosMediaPlayers |
| Qihoo-360 | 1.0.0.1015 | HEUR/QVM10.1.Malware.Gen |
| nProtect | 2014-10-06.01 | Trojan/W32.Agent.348056.B |
| Kaspersky | 15.0.1.10 | not-a-virus:AdWare.NSIS.Adwapper.do |
| Rising Antivirus | 25.0.0.17 | PE:Malware.Obscure!1.9C59 |
| Fortinet FortiGate | 5.1.152.0 | Riskware/CroRi |
| K7 AntiVirus | 9.188.14410 | Unwanted-Program ( 0040f9a31 ) |
| K7GW | 9.188.14407 | Unwanted-Program ( 0040f9a31 ) |
| Tencent | 1.0.0.1 | Win32.Adware.Bp-browser.Luqs |
| Kingsoft AntiVirus | 2013.4.9.267 | Win32.Troj.NSIS.cz.(kcloud) |
| Antiy-AVL | 1.0.0.1 | GrayWare[AdWare:not-a-virus]/NSIS.Adwapper |
How to Remove A8d80158-8a89-4bce-b3c5-45be4ebf96dd-4.exe
In case the removal of the a8d80158-8a89-4bce-b3c5-45be4ebf96dd-4.exe file is required, the ensuing steps should be adhered to. It's always important to be cautious when altering system files, as unintended modifications could trigger unforeseen system reactions.
-
Find the File: The initial step involves locating a8d80158-8a89-4bce-b3c5-45be4ebf96dd-4.exe on your system. The File Explorer search feature can assist you in doing this.
-
Secure Your Data: Always back up essential data before changing your system files. This is a critical safety step.
-
Eliminate the File: After identifying the location of a8d80158-8a89-4bce-b3c5-45be4ebf96dd-4.exe, you can delete it. Just right-click the file and select Delete. This action moves the file to your Recycle Bin.
-
Finalize the Deletion: To ensure a8d80158-8a89-4bce-b3c5-45be4ebf96dd-4.exe is completely eradicated from your system, you should empty your Recycle Bin. Right-click on the Recycle Bin and choose Empty Recycle Bin.
-
Verify System Health: Conduct a comprehensive system scan with a reliable antivirus tool once you've disposed of the file. This ensures there are no remnants of the file lurking in your system.
Note: It's important to mention that if a8d80158-8a89-4bce-b3c5-45be4ebf96dd-4.exe is associated with the a program, its removal may impact its functionality. If any issues arise post deletion, consider reinstalling the program or consult a technology professional for guidance.
Repair A8d80158-8a89-4bce-b3c5-45be4ebf96dd-4.exe Error Automatically
In this guide, we will fix a8d80158-8a89-4bce-b3c5-45be4ebf96dd-4.exe and other EXE errors automatically.
-
Click the Download Fortect button.
-
Save the Fortect setup file to your device.
-
Locate and double-click the downloaded setup file.
-
Follow the on-screen instructions to install Fortect.
Perform a Repair Install of Windows
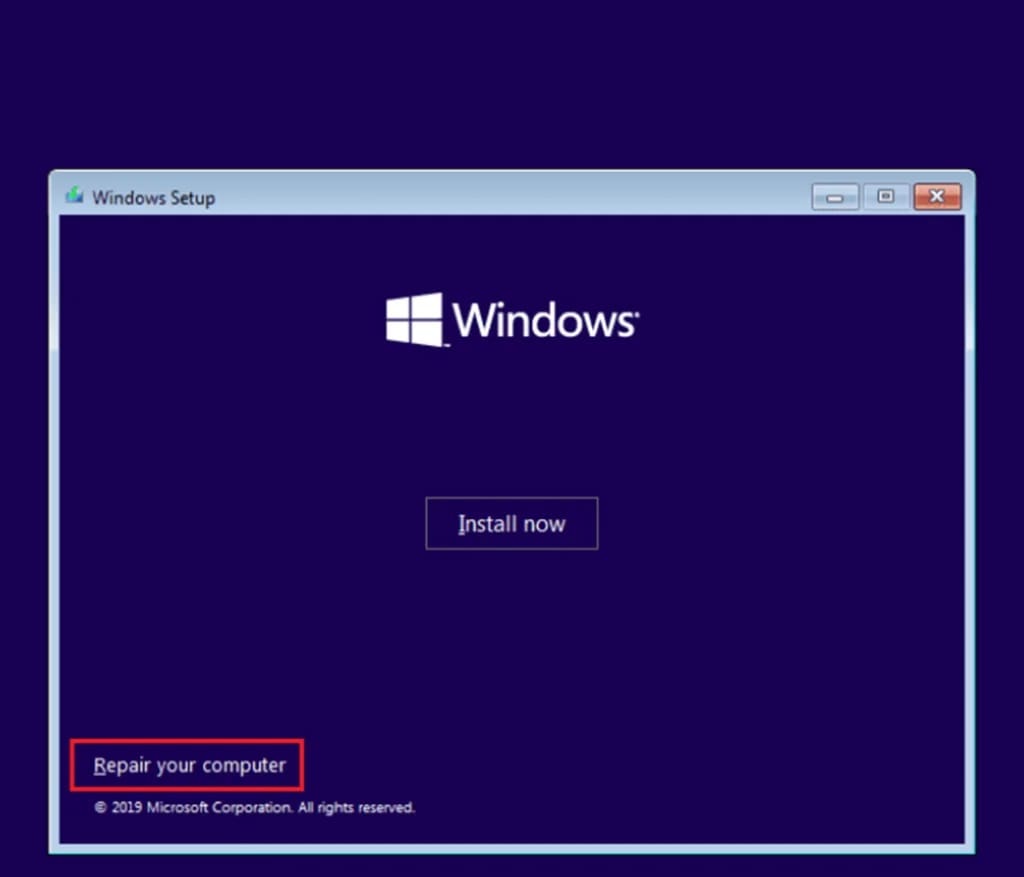
How to perform a repair install of Windows. A repair installation resets all Windows system files.
-
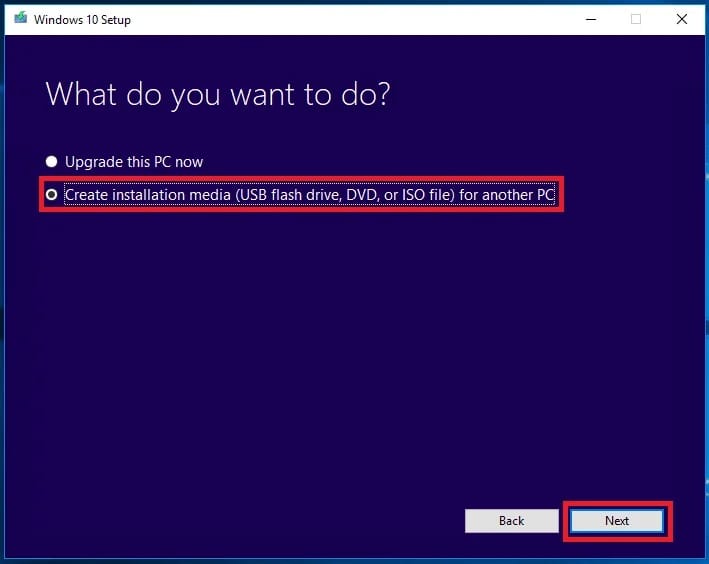
Go to the Microsoft website and download the Windows 10 Media Creation Tool.
-
Run the tool and select Create installation media for another PC.
-
Follow the prompts to create a bootable USB drive or ISO file.
-
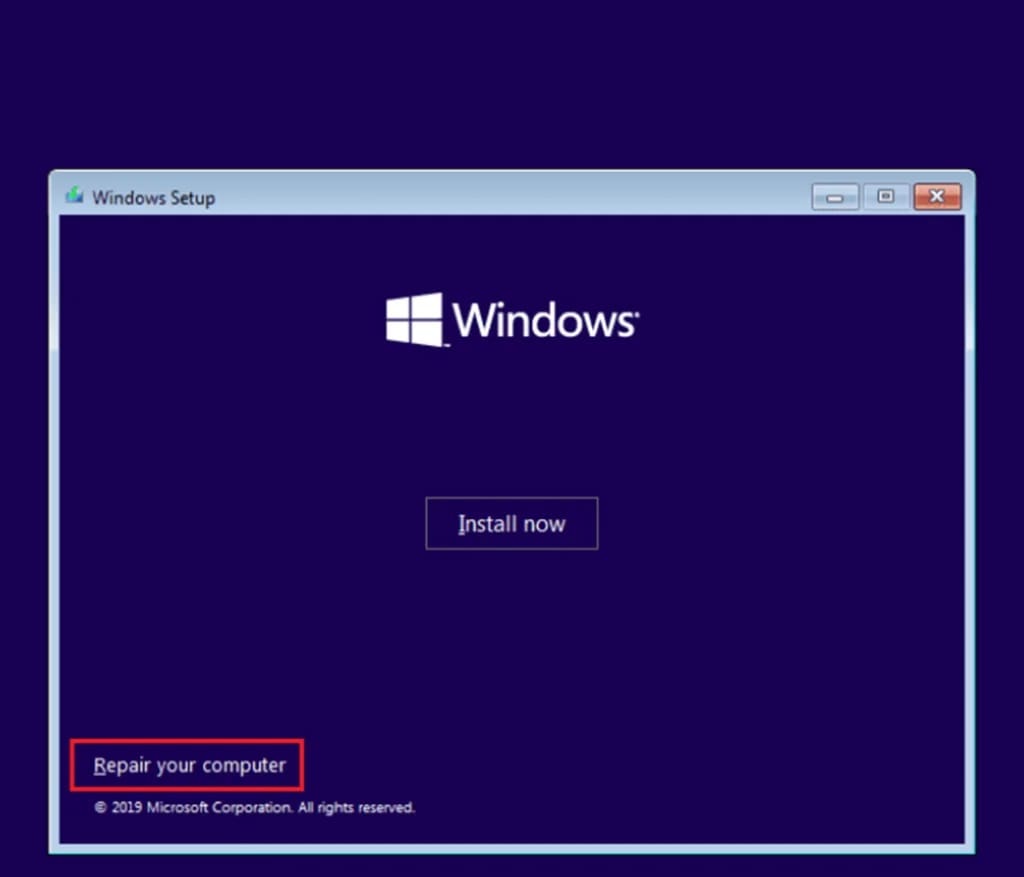
Insert the Windows 10 installation media you created into your PC and run setup.exe.
-
Follow the prompts until you get to the Ready to install screen.
-
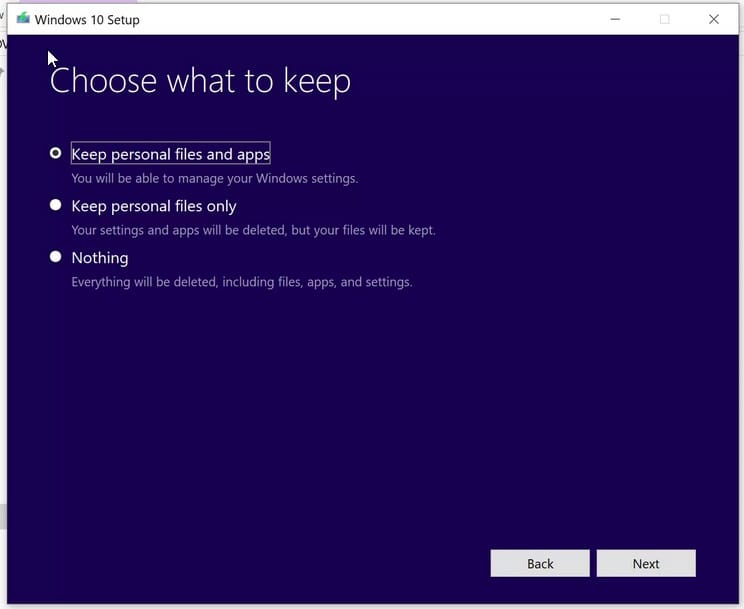
On the Ready to install screen, make sure Keep personal files and apps is selected.
-
Click Install to start the repair install.
-
Your computer will restart several times during the installation. Make sure not to turn off your computer during this process.
Run the Windows Check Disk Utility
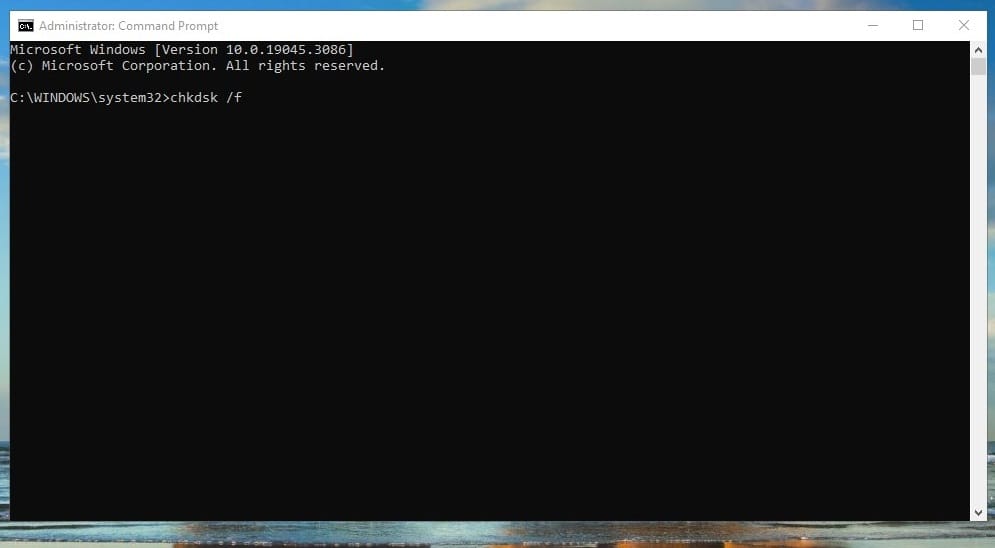
How to use the Windows Check Disk Utility. Scans your disk for a8d80158-8a89-4bce-b3c5-45be4ebf96dd-4.exe errors and automatically fix them.
-
Press the Windows key.
-
Type
Command Promptin the search bar and press Enter. -
Right-click on Command Prompt and select Run as administrator.
-
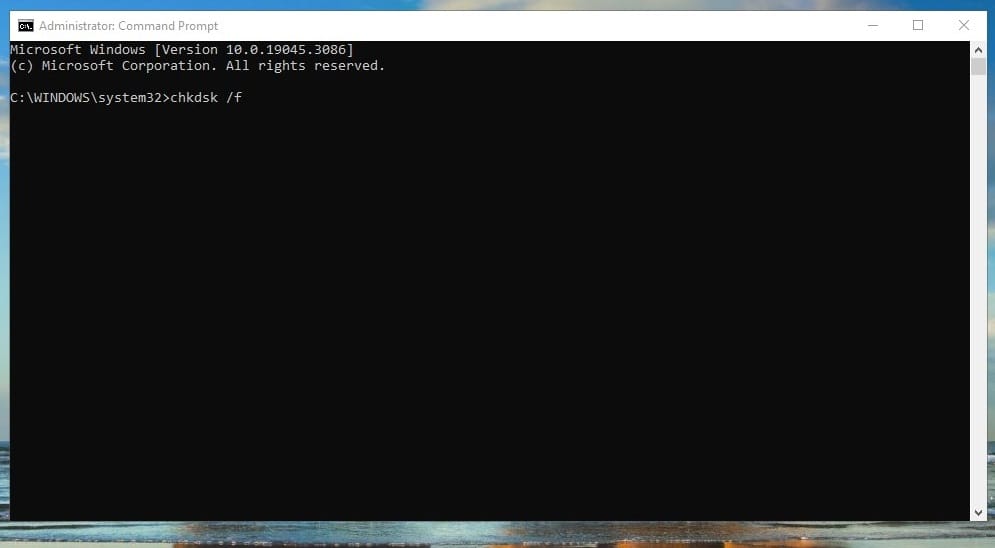
In the Command Prompt window, type
chkdsk /fand press Enter. -
If the system reports that it cannot run the check because the disk is in use, type
Yand press Enter to schedule the check for the next system restart.
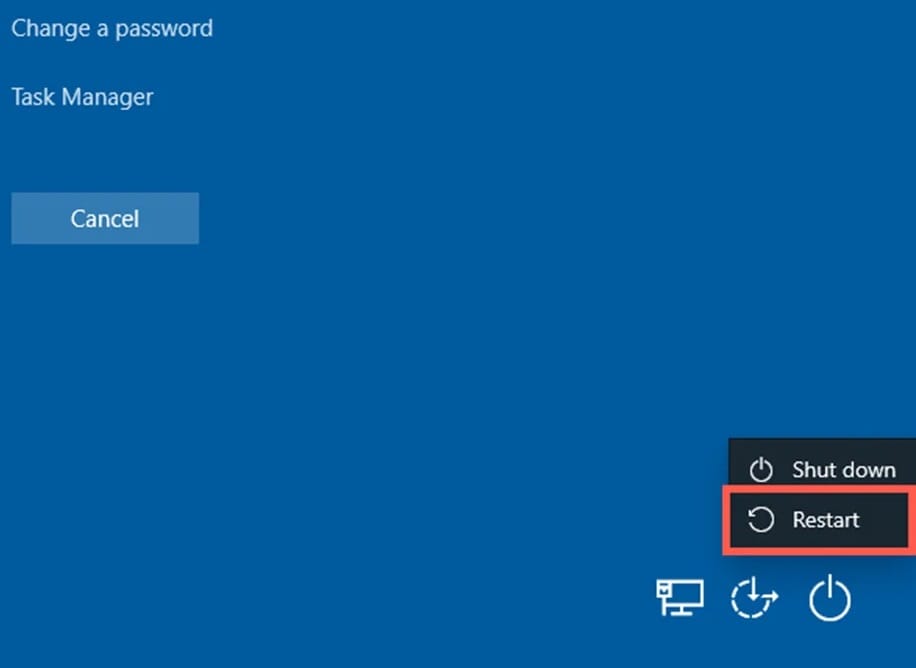
-
If you had to schedule the check, restart your computer for the check to be performed.
Software that installs a8d80158-8a89-4bce-b3c5-45be4ebf96dd-4.exe
| Software | File MD5 | File Version |
|---|---|---|
|
|
f619c6a8f3f6a4b8231a52c1aedd36e2 | 1.35.9.16 |

