Recommended: Use Fortect System Repair to repair 2e18c836-5212-44f2-b4dd-c1ea360752fb-5.exe errors. This repair tool has been proven to identify and fix errors and other Windows problems with high efficiency. Download Fortect here.
- ✓
Are you having trouble opening a file with a .exe extension? You're in the right place. We'll cover common issues, how to troubleshoot them, and what to do if your file is infected with malware.
We'll also guide you on how to uninstall the software associated with the .exe file. Let's get started and troubleshoot that file together.
Common 2e18c836-5212-44f2-b4dd-c1ea360752fb-5.exe Errors on Windows
Confronting errors linked to 2e18c836-5212-44f2-b4dd-c1ea360752fb-5.exe can be a daunting task due to the diversity of underlying causes, which might include software incompatibility, obsolete drivers, or even malware presence. In the section below, we've enumerated the most frequently encountered errors related to 2e18c836-5212-44f2-b4dd-c1ea360752fb-5.exe in order to assist you in comprehending and potentially rectifying the issues.
- Application Not Found: This message occurs when the system can't find the necessary application. Possible reasons could be the application being deleted, moved, or an inaccurately specified file path.
- Access is Denied: This error message appears when the system refuses permission to a file or resource. This might occur due to insufficient user privileges, file ownership issues, or restrictive file permissions.
- Unable to Start Correctly (0xc000007b): This warning is shown when the application fails to start as it should, typically caused by an inconsistency between the 32-bit and 64-bit versions of the application and the Windows operating system.
- Not a Valid Win32 Application: This error message signifies that the program is incompatible with the Windows version in use, or the program file could be damaged.
- Runtime Errors: This error message occurs when a program encounters a problem during its execution. This could be due to issues like software bugs, memory leaks, or conflicts with other running programs.
File Analysis: Is 2e18c836-5212-44f2-b4dd-c1ea360752fb-5.exe a Virus?
The file 2e18c836-5212-44f2-b4dd-c1ea360752fb-5.exe poses potential safety concerns, having been flagged by 49 different virus detection tools. This report underscores the need for caution when dealing with this file, as risks may include unauthorized data access and compromised system performance.
While 2e18c836-5212-44f2-b4dd-c1ea360752fb-5.exe is a part of a software program, its potential risks should not be overlooked
The priority is to address these security issues promptly.
Recommended Protection: Fortect
We recommend Fortect, a well-regarded malware scanner, to protect your system. Download the application, and conduct a thorough system scan. This action step will help identify and rectify issues associated with harmful files like 2e18c836-5212-44f2-b4dd-c1ea360752fb-5.exe, bolstering the health of your computer.
Multiple virus scanners have detected possible malware in 1 variations of 2e18c836-5212-44f2-b4dd-c1ea360752fb-5.exe.
| Scanner Software | Version | Result |
|---|---|---|
| Lavasoft Ad-Aware | 12.0.163.0 | Gen:Application.Heur.Eu1@m4LT03eO |
| AhnLab-V3 | 2015.04.11.00 | Win-PUP/CrossRider |
| Antiy-AVL | 1.0.0.1 | Trojan/NSIS.GoogUpdate.cr |
| avast! | 8.0.1489.320 | Win32:Crossrider-AG [PUP] |
| AVG | 15.0.0.4328 | Crossrider.CQU |
| Avira | 3.6.1.96 | ADWARE/CrossRider.Gen2 |
| AVware | 1.5.0.21 | Crossrider (fs) |
| Baidu-International | 3.5.1.41473 | Adware.Win32.CrossAd.AV |
| Bitdefender | 7.2 | Gen:Application.Heur.Eu1@m4LT03eO |
| Bkav FE | 1.3.0.6379 | W32.HfsAdware.CC2C |
| CAT-QuickHeal | 14.00 | PUA.GoogleUpdate.A5 |
| Clam AntiVirus | 0.98.5.0 | Win.Adware.Agent-8513 |
| Comodo Security | 21724 | ApplicUnwnt |
| Cyren | 5.4.16.7 | W32/S-9ad4719b!Eldorado |
| Dr.Web | 7.0.12.3050 | Trojan.Crossrider.30989 |
| ESET-NOD32 | 11458 | a variant of Win32/Toolbar.CrossRider.AV potentially unwanted |
| Fortinet FortiGate | 5.0.999.0 | W32/GoogUpdate.AH!tr |
| F-Prot | 4.7.1.166 | W32/S-9ad4719b!Eldorado |
| F-Secure | 11.0.19100.45 | Gen:Application.Heur.Eu1@m4LT03eO |
| G Data | 25 | Gen:Application.Heur.Eu1@m4LT03eO |
| Jiangmin | 16.0.100 | AdWare/NSIS.ajm |
| K7 AntiVirus | 9.202.15559 | Unwanted-Program ( 004a9d091 ) |
| K7GW | 9.202.15559 | Unwanted-Program ( 004a9d091 ) |
| Kaspersky | 15.0.1.10 | Trojan.NSIS.GoogUpdate.cr |
| Kingsoft AntiVirus | 2013.4.9.267 | Win32.Troj.NSIS.cr.(kcloud) |
| McAfee | 6.0.5.614 | Artemis!D512431295A8 |
| MicroWorld-eScan | 12.0.250.0 | Gen:Application.Heur.Eu1@m4LT03eO |
| NANO AntiVirus | 0.30.10.952 | Trojan.Win32.GoogUpdate.deczgs |
| Panda Antivirus | 4.6.4.2 | Trj/Genetic.gen |
| Qihoo-360 | 1.0.0.1015 | Win32/Trojan.3b1 |
| Rising Antivirus | 25.0.0.17 | PE:Malware.Obscure!1.9C59 |
| Sophos | 4.98.0 | weDownload Manager |
| Symantec | 20141.2.0.56 | Trojan.Gen.2 |
| Tencent | 1.0.0.1 | Trojan.Win32.Qudamah.Gen.6 |
| Trend Micro | 9.740.0.1012 | TROJ_GEN.R0C1C0ELQ14 |
| TrendMicro-HouseCall | 9.700.0.1001 | TROJ_GEN.R0C1C0ELQ14 |
| VIPRE Antivirus | 39242 | Crossrider (fs) |
| Zillya | 2.0.0.2135 | Trojan.GoogUpdate.Win32.305 |
| Emsisoft Anti-Malware | 3.0.0.600 | Gen:Variant.Adware.Plush.2 (B) |
| McAfee-GW-Edition | v2014.2 | BehavesLike.Win32.Trojan.gh |
| nProtect | 2014-11-03.01 | Trojan-Clicker/W32.Agent.477544 |
| IKARUS anti.virus | T3.1.7.8.0 | Trojan.GoogUpdate |
| Malwarebytes | 1.75.0.1 | PUP.Optional.CrossRider.A |
| Vba32 AntiVirus | 3.12.26.3 | AdWare.Adwapper |
| Agnitum Outpost | 5.5.1.3 | PUA.Toolbar.CroRi! |
| ALYac | 1.0.1.4 | Adware.Crossrider.V |
| Arcabit | 1.0.0.425 | Adware.Crossrider.V |
| Avira AntiVir | 7.11.169.144 | Adware/Kazy.374062.127 |
| SUPERAntiSpyware | 5.6.0.1032 | Adware.Crossrider/Variant |
How to Remove 2e18c836-5212-44f2-b4dd-c1ea360752fb-5.exe
In case the removal of the 2e18c836-5212-44f2-b4dd-c1ea360752fb-5.exe file is required, the ensuing steps should be adhered to. It's always important to be cautious when altering system files, as unintended modifications could trigger unforeseen system reactions.
-
Find the File: The initial step involves locating 2e18c836-5212-44f2-b4dd-c1ea360752fb-5.exe on your system. The File Explorer search feature can assist you in doing this.
-
Secure Your Data: Always back up essential data before changing your system files. This is a critical safety step.
-
Eliminate the File: After identifying the location of 2e18c836-5212-44f2-b4dd-c1ea360752fb-5.exe, you can delete it. Just right-click the file and select Delete. This action moves the file to your Recycle Bin.
-
Finalize the Deletion: To ensure 2e18c836-5212-44f2-b4dd-c1ea360752fb-5.exe is completely eradicated from your system, you should empty your Recycle Bin. Right-click on the Recycle Bin and choose Empty Recycle Bin.
-
Verify System Health: Conduct a comprehensive system scan with a reliable antivirus tool once you've disposed of the file. This ensures there are no remnants of the file lurking in your system.
Note: It's important to mention that if 2e18c836-5212-44f2-b4dd-c1ea360752fb-5.exe is associated with the a program, its removal may impact its functionality. If any issues arise post deletion, consider reinstalling the program or consult a technology professional for guidance.
Repair 2e18c836-5212-44f2-b4dd-c1ea360752fb-5.exe Error Automatically
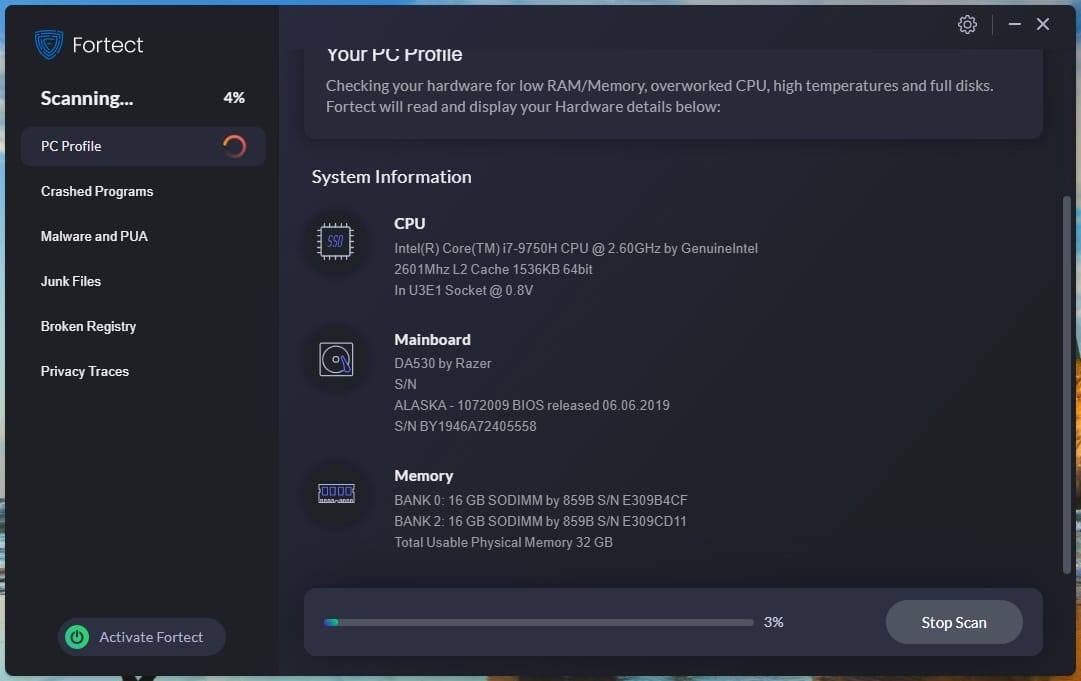
In this guide, we will fix 2e18c836-5212-44f2-b4dd-c1ea360752fb-5.exe and other EXE errors automatically.
-
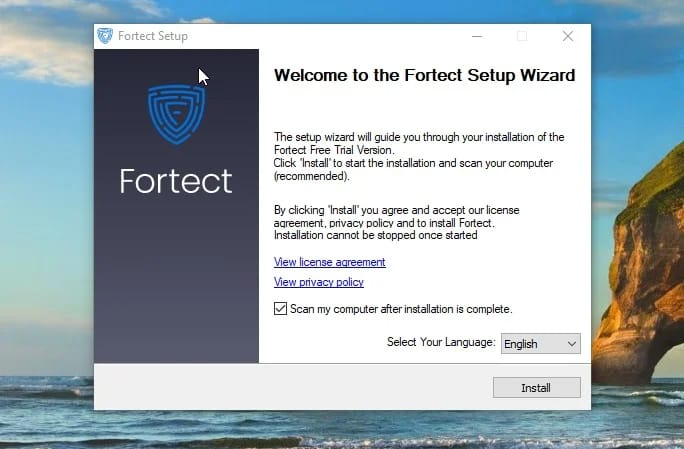
Click the Download Fortect button.
-
Save the Fortect setup file to your device.
-
Locate and double-click the downloaded setup file.
-
Follow the on-screen instructions to install Fortect.
Run the Deployment Image Servicing and Management (DISM) to Fix the 2e18c836-5212-44f2-b4dd-c1ea360752fb-5.exe Error
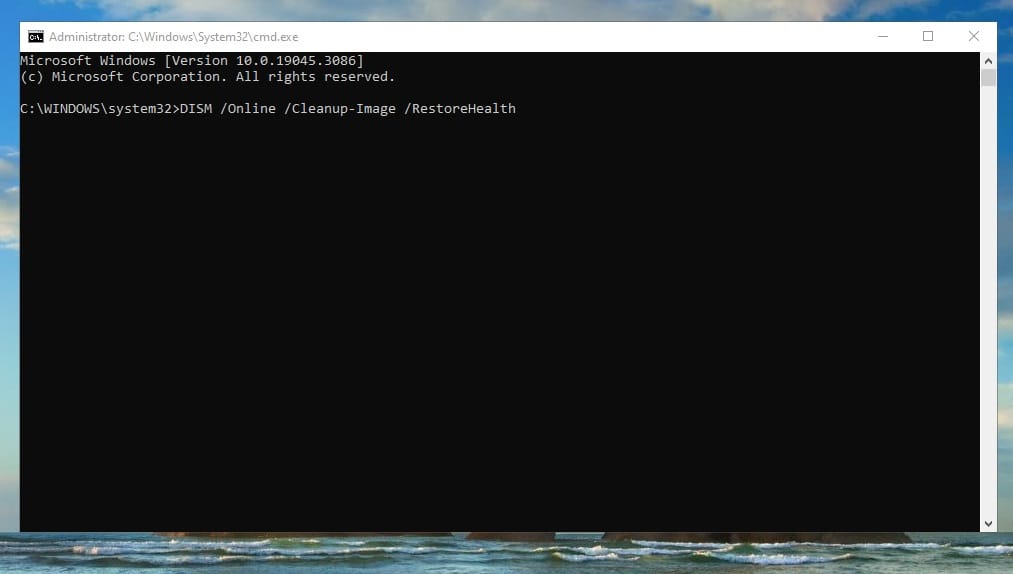
In this guide, we will aim to resolve issues related to 2e18c836-5212-44f2-b4dd-c1ea360752fb-5.exe by utilizing the Deployment Image Servicing and Management (DISM) tool to scan and repair Windows system files.
-
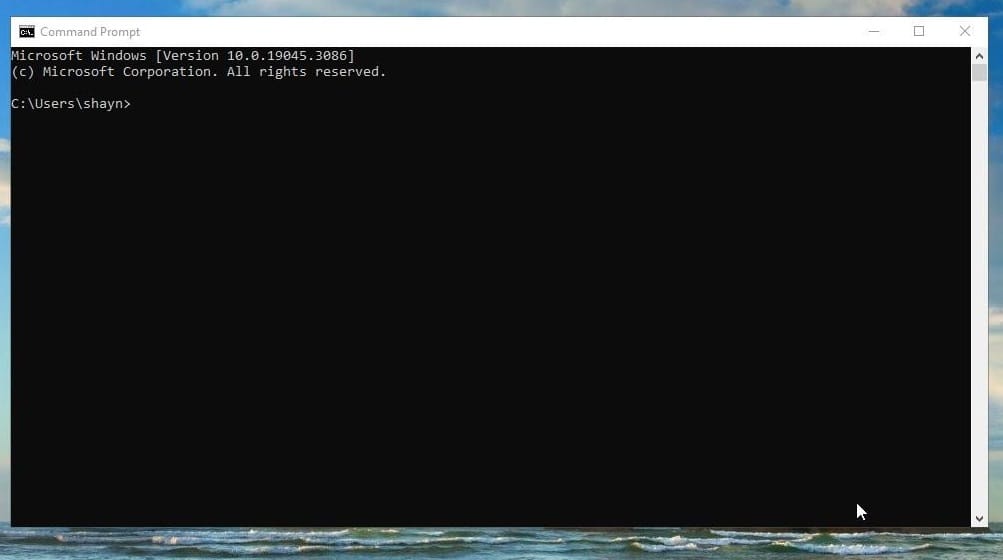
Press the Windows key.
-
Type
Command Promptin the search bar. -
Right-click on Command Prompt and select Run as administrator.
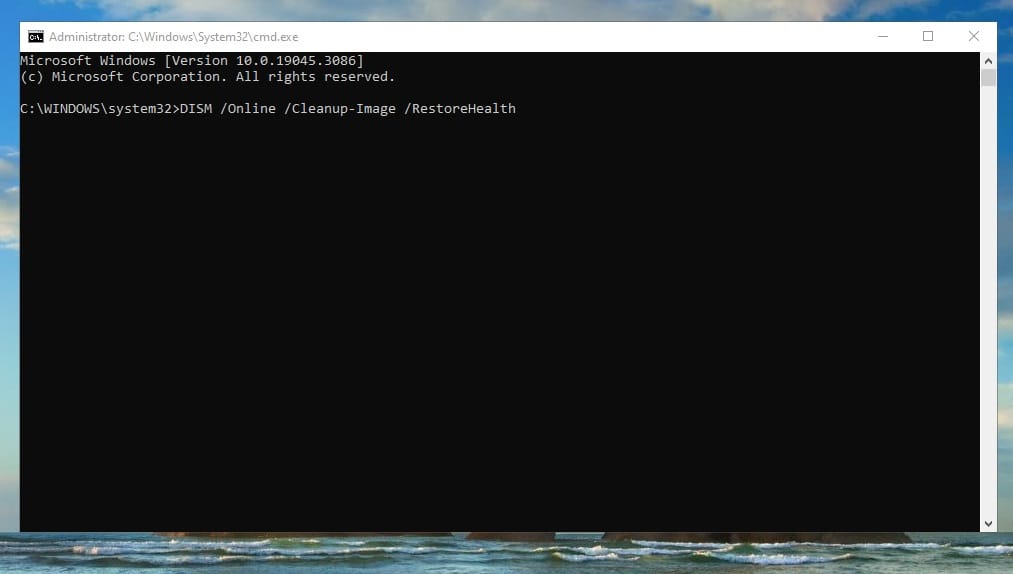
-
In the Command Prompt window, type
DISM /Online /Cleanup-Image /RestoreHealthand press Enter. -
Allow the Deployment Image Servicing and Management tool to scan your system and correct any errors it detects.
Perform a Repair Install of Windows
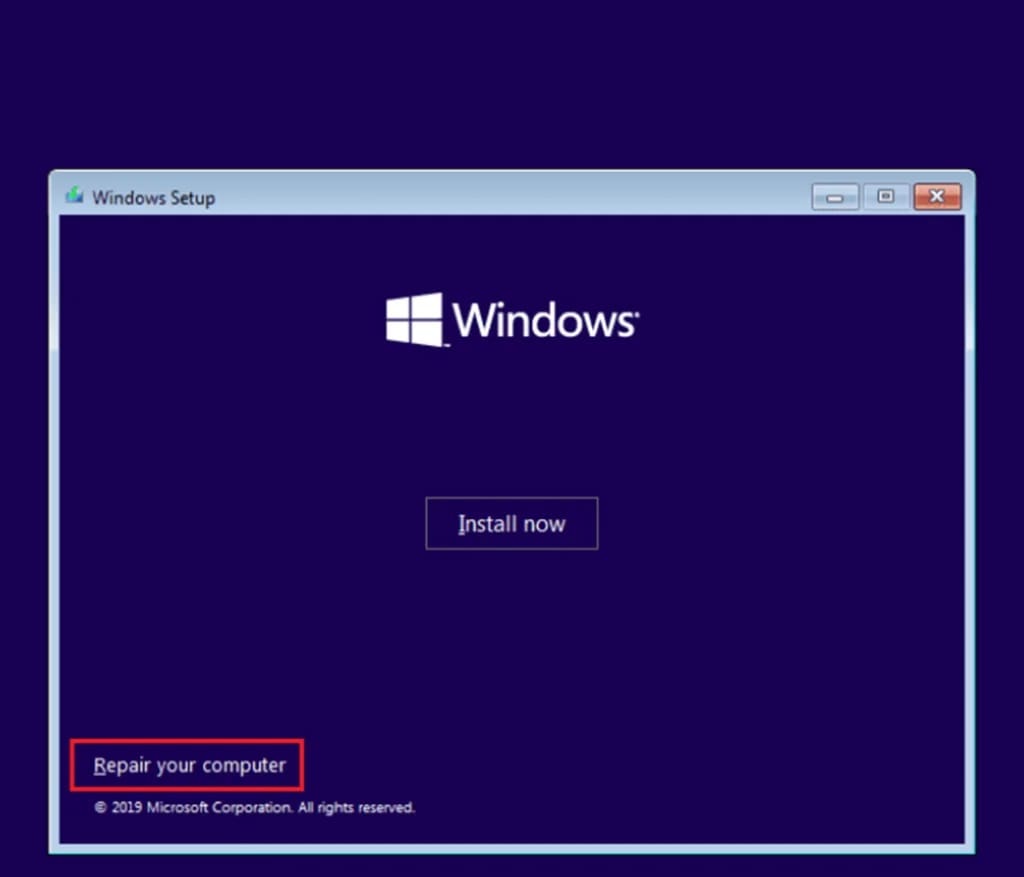
How to perform a repair install of Windows. A repair installation resets all Windows system files.
-
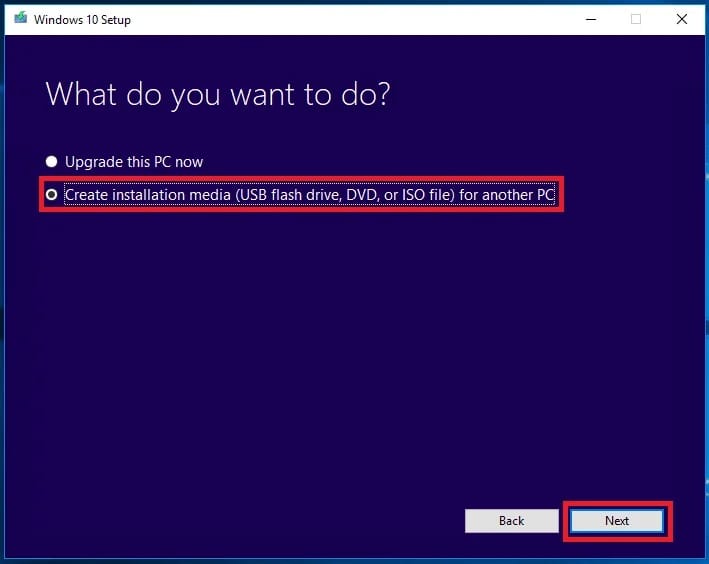
Go to the Microsoft website and download the Windows 10 Media Creation Tool.
-
Run the tool and select Create installation media for another PC.
-
Follow the prompts to create a bootable USB drive or ISO file.
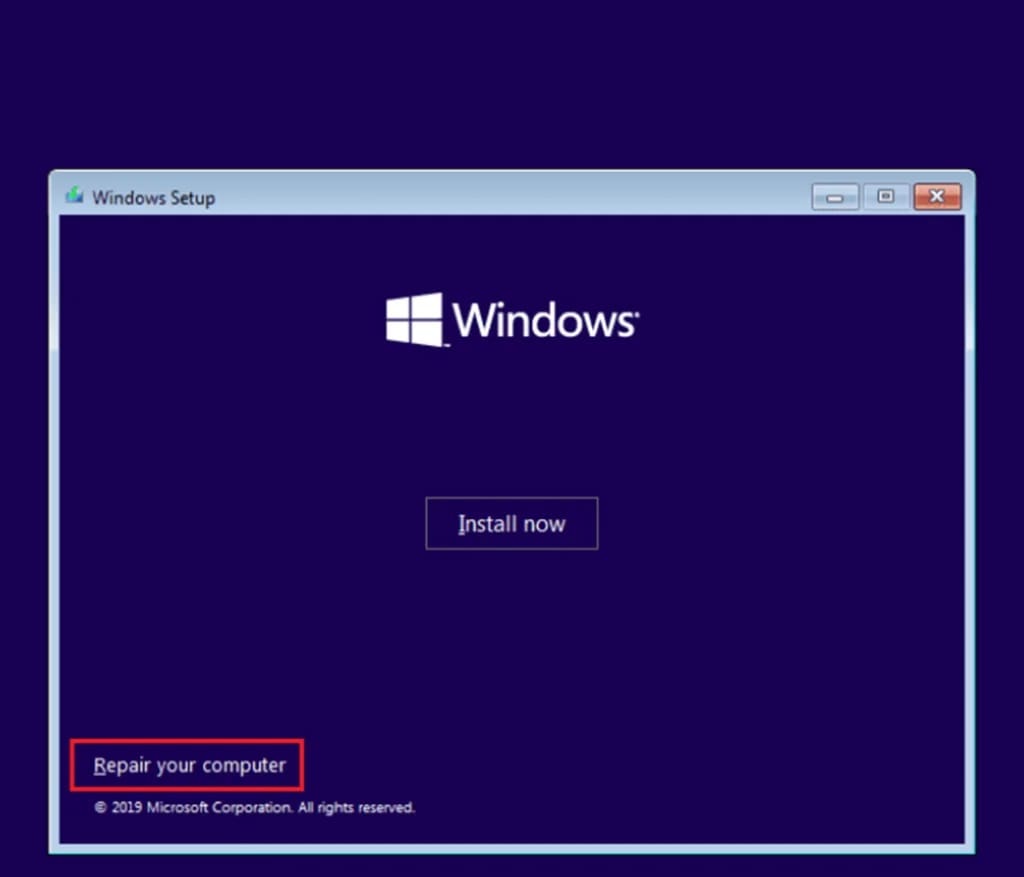
-
Insert the Windows 10 installation media you created into your PC and run setup.exe.
-
Follow the prompts until you get to the Ready to install screen.
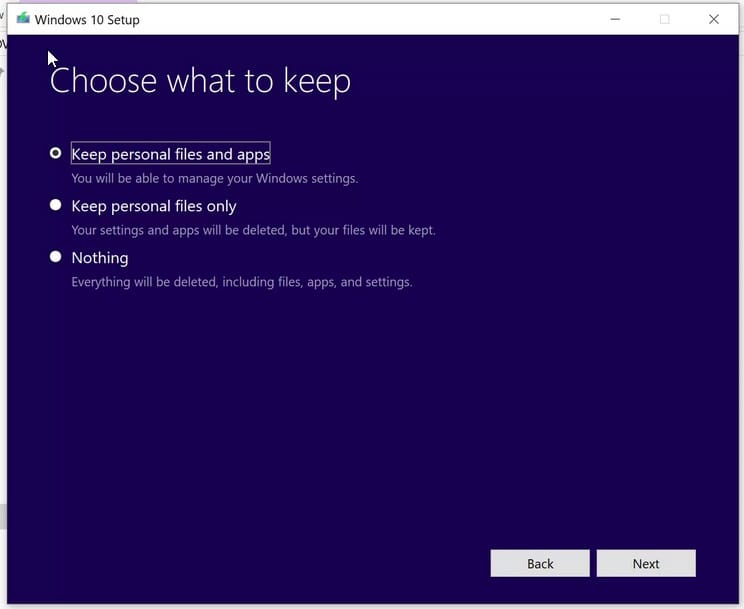
-
On the Ready to install screen, make sure Keep personal files and apps is selected.
-
Click Install to start the repair install.
-
Your computer will restart several times during the installation. Make sure not to turn off your computer during this process.
Software that installs 2e18c836-5212-44f2-b4dd-c1ea360752fb-5.exe
| Software | File MD5 | File Version |
|---|---|---|
|
|
d512431295a86ff272909cbc734faca2 | 1.34.2.13 |


